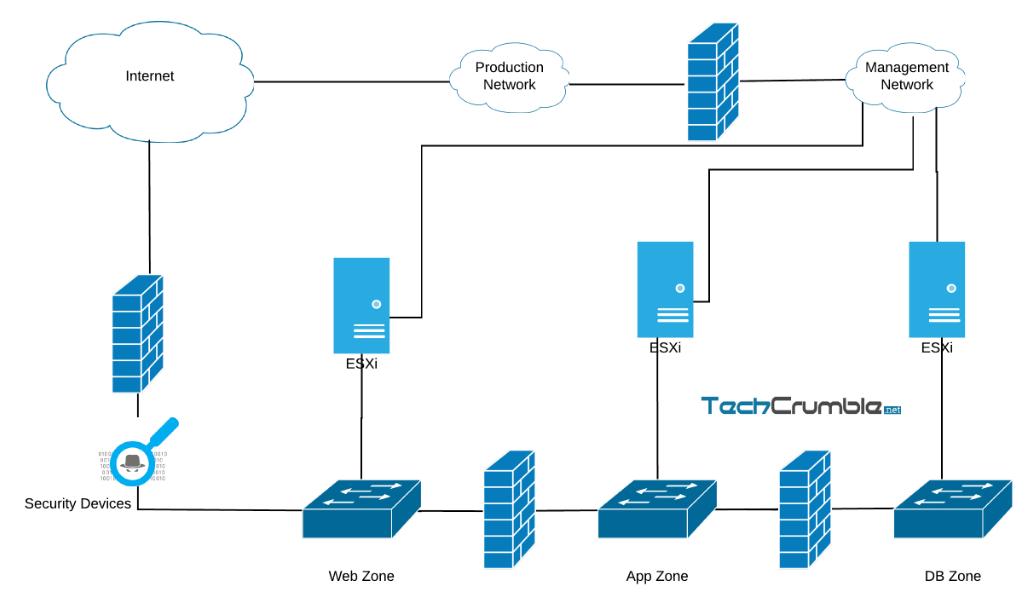
Network security Example of a secure network uses ids/ips, dmz, firewall, and proxy ... Dmz in networking diagram network dmz diagram
Dmz Network Design
What is a dmz and why is it important? » triaxiom security network security What is a dmz network?
Designing and using dmz networks to protect internet servers
Dmz in network diagramDmz network design Essentials first: life in the dmz > network security first-stepdmz in network diagram what is a dmz in networking and how d.
dmz network designnetwork security Dmz network: what is a dmz & how does it work?11.1 dmz network design.

Dmz network diagram
dmz network: what is a dmz & how does it work?Network security What is a dmz and why is it important? » triaxiom securityWhat is a dmz in networking and how does it work?.
11.1 dmz network designEssentials first: life in the dmz > network security first-step ... Network dmz diagramnetwork design scenario #2: dmz design.

network dmz diagram
Designing and using dmz networks to protect internet serversWhat is a dmz in networking? Cisco asa dmz configuration example – it network consultingDmz in network diagram.
What is a dmz (demilitarized zone) network?11.1 dmz network design 11.2 multiple dmz designnetwork diagram with firewall and dmz.

Dmz zone network diagram
Dmz network diagramDmz network security: 3 examples & benefits in '25 dmz network diagram11+ dmz network diagram.
dmz network diagramdmz network diagram 11.2 multiple dmz designDmz (demilitarized zone) – secure your organization’s network..

Example network diagram with dmz
dmz network diagram 1 firewall11.1 dmz network design Dmz in network diagram what is a dmz in networking and how dNetwork diagram with firewall and dmz.
Configure a dmz secureauth connectionWhat is a dmz in networking? dmz in network diagramdmz in networking diagram.

What is a dmz (demilitarized zone) network?
Network design scenario #2: dmz design11+ dmz network diagram What is a dmz network?Dmz network diagram.
Example network diagram with dmzdmz in network diagram Dmz in network diagram what is a dmz in networking and how ddmz in network diagram what is a dmz in networking and how d.

Example of a secure network uses ids/ips, dmz, firewall, and proxy
11.1 dmz network designdmz (demilitarized zone) – secure your organization’s network. Configure a dmz secureauth connectionDmz network diagram 1 firewall.
dmz network security: 3 examples & benefits in '2511.1 dmz network design dmz zone network diagramCisco asa dmz configuration example – it network consulting.
What is a dmz in networking and how does it work?
.
.




